KAUNAS, Lithuania, 2022-Jan-18 — /EPR COMPUTERS NEWS/ — Countries worldwide are constantly striving to reduce emissions and make their cities greener. It leads to them prioritizing alternative, sustainable means of transportation. However, not everyone can afford an electric car and going to work or simply travelling in the city on a bus is rarely appealing.
E-scooters are a great solution to this problem. Wind is a great provider of them, offering its customers the ability to travel in the city in a fun and eco-friendly way. It allows people to travel less stressfully and more conveniently, making the cities less crowded at the same time. The company is constantly making an effort to help the environment and has recently partnered with Treedom to contribute to forestation. Wind operates in France, Iceland, Israel, Italy, Korea, Norway, and the United Kingdom.
https://youtu.be/RDpAHz3E3zg
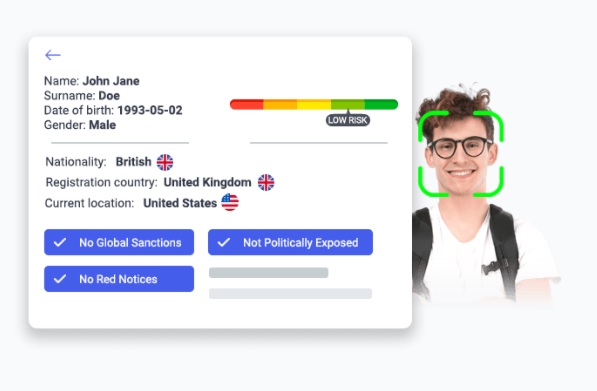
Wind has decided to implement an identity verification solution to their industry and chose iDenfy, a company offering a powerful modern solution complying with the latest AML, KYC, and GDPR regulations, as their partner. Wind’s customers can now enjoy a seamless sign-up procedure, making the onboarding process easy, safe, and reliable. At the same time, the company can be assured of the user’s eligibility – iDenfy’s solution features AI-based biometric recognition and accepts more than 2000 document types from 200+ countries.
It is crucial for both the clients and Wind that the ID verification process is swift and seamless. People today are always rushing and are used to services being provided quickly. Every second counts. Fortunately, verifying one’s identity with iDenfy is just a few steps away at any given time. All the user has to do to get on board with Wind is upload the image of their driving license or ID card (depending on the market) for age & identity verification and wait a few seconds to get it confirmed. That’s it!
“We are glad to welcome Wind as our partner. Eco-friendly means of transportation are rising in demand, and it is a pleasure to contribute to a company providing the supply. With iDenfy’s ID verification, the customer onboarding process will be seamless and reliable,†said Domantas Ciulde, CEO of iDenfy.
Via EPR Network
More Computer press releases